
Android malware builders are stepping up their billing fraud recreation with applications that disable Wi-Fi connections, surreptitiously subscribe end users to pricey wi-fi companies, and intercept text messages, all in a bid to gather significant fees from unsuspecting consumers, Microsoft claimed on Friday.
This danger class has been a fact of lifestyle on the Android platform for a long time, as exemplified by a family of malware acknowledged as Joker, which has contaminated millions of phones due to the fact 2016. Despite consciousness of the issue, minimal awareness has been paid out to the methods that these kinds of “toll fraud” malware takes advantage of. Enter Microsoft, which has revealed a technological deep dive on the situation.
The billing system abused in this style of fraud is WAP, brief for wi-fi application protocol, which presents a implies of accessing details in excess of a cellular community. Cellular cell phone customers can subscribe to this kind of providers by traveling to a service provider’s web site although their gadgets are related to mobile support, then clicking a button. In some cases, the provider will reply by texting a one particular-time password (OTP) to the phone and requiring the consumer to deliver it back in buy to confirm the subscription request. The method looks like this:
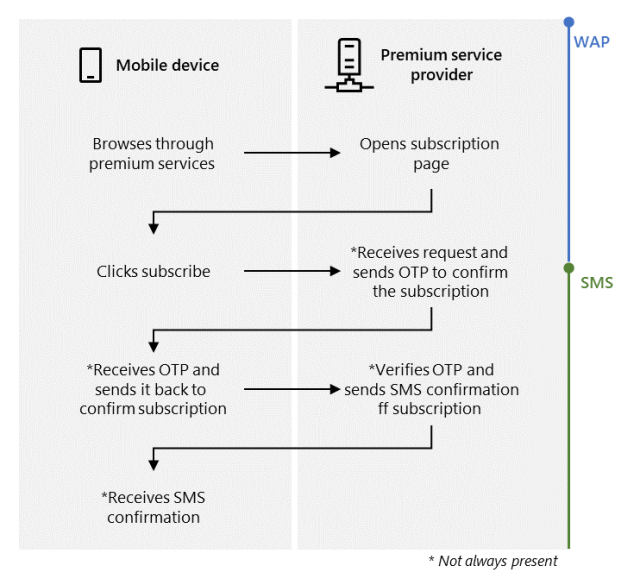
Microsoft
The intention of the malicious applications is to subscribe contaminated telephones to these WAP products and services automatically, with no the recognize or consent of the owner. Microsoft stated that malicious Android applications its researchers have analyzed obtain this goal by following these methods:
- Disable the Wi-Fi relationship or wait for the user to swap to a mobile community
- Silently navigate to the membership site
- Automobile-simply click the membership button
- Intercept the OTP (if relevant)
- Send the OTP to the services service provider (if applicable)
- Cancel the SMS notifications (if relevant)
Malware builders have different strategies to force a cellular phone to use a mobile link even when it’s related to Wi-Fi. On products working Android 9 or before, the builders can invoke the setWifiEnabled method of the WifiManager course. For versions 10 and previously mentioned, builders can use the requestNetwork functionality of the ConnectivityManager course. At some point, phones will load details exclusively in excess of the mobile network, as shown in this impression:
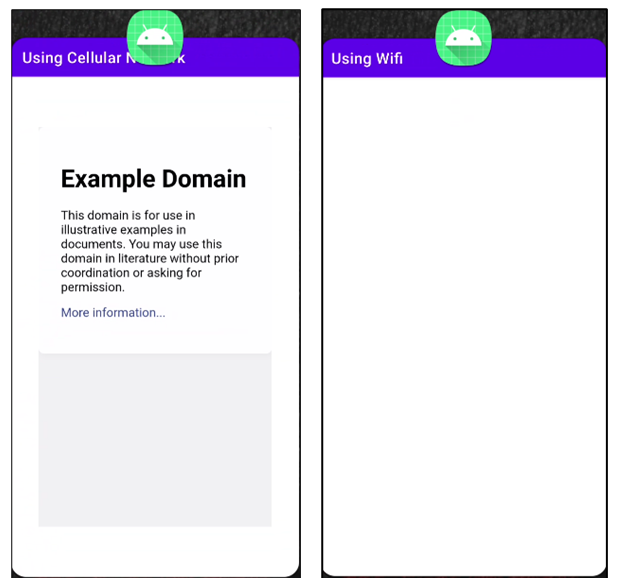
Microsoft
The moment a mobile phone utilizes the cellular community for details transmission, the destructive application surreptitiously opens a browser in the background, navigates to the WAP membership webpage, and clicks a subscribe button. Confirming the membership can be difficult because affirmation prompts can come by SMS, HTTP, or USSD protocols. Microsoft lays out specific solutions that malware builders can use to bypass each individual sort of affirmation. The Microsoft article then goes on to clarify how the malware suppresses periodic messages that the subscription company may possibly mail the person to remind them of their subscription.
“By subscribing buyers to high quality expert services, this malware can guide to victims acquiring considerable mobile monthly bill expenses,” Microsoft scientists wrote. “Affected units also have increased danger for the reason that this danger manages to evade detection and can attain a high variety of installations in advance of a solitary variant gets taken off.”
Google actively bars applications from its Participate in marketplace when it detects indicators of fraud or malice, or when it receives stories of malicious apps from 3rd functions. Whilst Google generally doesn’t take away destructive applications until finally immediately after they have contaminated tens of millions of consumers, apps downloaded from Perform are frequently regarded as much more reputable than apps from 3rd-social gathering marketplaces.




